How to Install Wildcard Certificate on Cisco Prime Infrastructure
I need to install a wildcard certificate on Cisco PI for testing purpose, the following is the installation process.
Environment
- Ubuntu 19.10
- OpenSSL 1.1.1c
- Prime Infrastructure 3.10
- Google Chrome 109.0.5414.120/Microsoft Edge 109.0.1518.70
- FTP Server
Generate certificate
We need to preconfigure [openssl.cnf] file, which is required for wildcard certificates. If there is no SAN(subjectAltName) information in the wildcard certificate, the browser will return ERR_CERT_COMMON_NAME_INVALID error.
The directory of the [openssl.cnf] file may be different in different operating systems, you can use the find command to find it.
root@ubuntu:/home/cisco/cert# find /usr/lib -name openssl.cnf /usr/lib/ssl/openssl.cnf
What we need to edit is [v3_req] and [alt_names], where the wildcard domain name is [*.pi.com], which is a domain name for local testing.
[ v3_req ] # Extensions to add to a certificate request basicConstraints = CA:FALSE keyUsage = nonRepudiation, digitalSignature, keyEncipherment subjectAltName = @alt_names [alt_names] DNS.1 = pi.com DNS.2 = *.pi.com
Then use openssl to generate a certificate.
openssl genrsa -out prime.key 2048 openssl rsa -in prime.key -out prime-key.pem openssl req -new -key prime-key.pem -out prime-request.csr openssl x509 -req -extensions v3_req -days 365 -in prime-request.csr -signkey prime.key -out prime-cert.cer -extfile /usr/lib/ssl/openssl.cnf
The following is the configuration process.
root@ubuntu:/home/cisco/cert# openssl req -new -key prime-key.pem -out prime-request.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [AU]:JP State or Province Name (full name) [Some-State]:Tokyo Locality Name (eg, city) []:Tokyo Organization Name (eg, company) [Internet Widgits Pty Ltd]:Company-Dummy Organizational Unit Name (eg, section) []:Unit-Dummy Common Name (e.g. server FQDN or YOUR name) []:*.pi.com Email Address []:dummy@pi.com Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []:cisco An optional company name []: root@ubuntu:/home/cisco/cert# root@ubuntu:/home/cisco/cert# root@ubuntu:/home/cisco/cert# root@ubuntu:/home/cisco/cert# openssl x509 -req -extensions v3_req -days 365 -in prime-request.csr -signkey prime.key -out prime-cert.cer -extfile /usr/lib/ssl/openssl.cnf Signature ok subject=C = JP, ST = Tokyo, L = Tokyo, O = Company-Dummy, OU = Unit-Dummy, CN = *.pi.com, emailAddress = dummy@pi.com Getting Private key root@ubuntu:/home/cisco/cert#
Import the certificate into Prime Infrastructure
Repository is used to configure server information to download certificate.
pi310/admin# conf t Enter configuration commands, one per line. End with CNTL/Z. pi310/admin(config)# repository test pi310/admin(config-Repository)# url ftp://192.1.1.1 pi310/admin(config-Repository)# user username password plain pw pi310/admin(config-Repository)# end
Upload the generated certificate to the FTP server and import the certificate on Prime Infrastructure.
pi310/admin# ncs key importkey prime.key prime-cert.cer repository test Imported server key. Changes will take effect on the next server restart pi310/admin# ncs key importsignedcert prime-cert.cer repository test Imported server certificate. Changes will take effect on the next server restart pi310/admin#
If everything is working fine, we need to restart ncs for the certificate to take effect. Note that restarting will take a long time.
pi310/admin# pi310/admin# ncs stop Stopping Prime Infrastructure... This may take a few minutes... Prime Infrastructure successfully shutdown. Stopping SAM daemon... Checking for SAM daemon again ... SAM Daemon not found... Stopping DA daemon ... Checking for DA daemon again ... DA Daemon not found... Completed shutdown of all services pi310/admin# ncs start Starting Prime Infrastructure... This may take a while (10 minutes or more) ... Prime Infrastructure started successfully. Redirecting to /bin/systemctl restart rsyslog.service Completed in 1240 seconds pi310/admin#
Verification
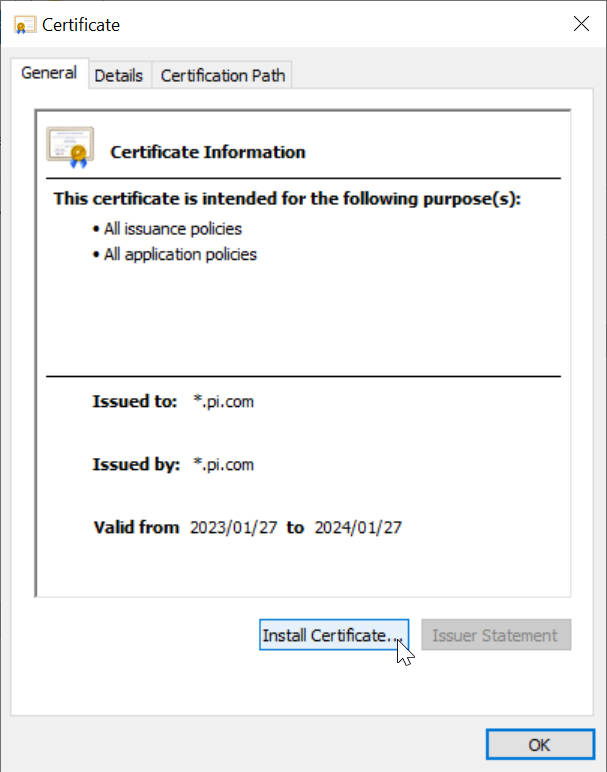
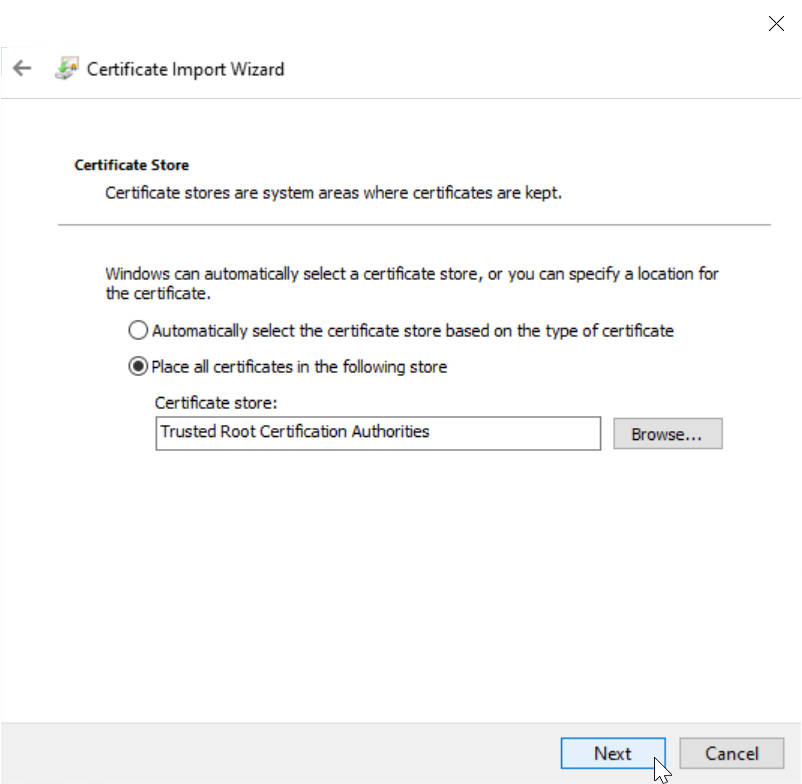
Install the certificate to the PC.
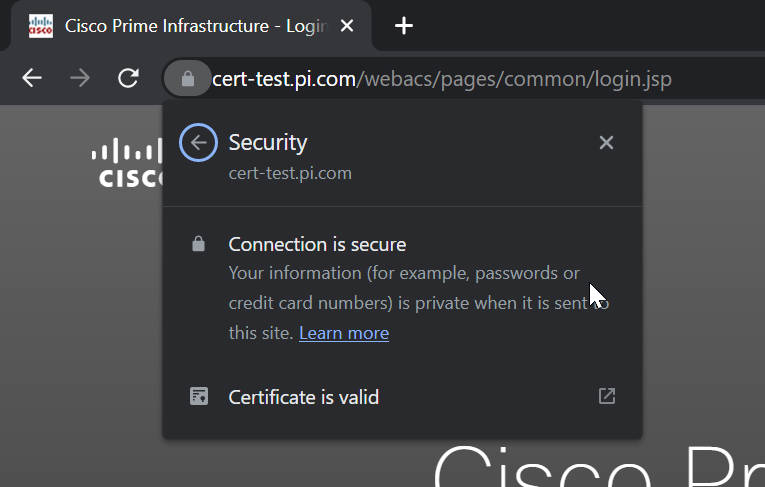
We also need a DNS server for domain name resolution. Since I’m just using it for testing, I configured the hosts file on my PC to solve this problem.
The hosts file is in the C:\Windows\System32\drivers\etc directory, after opening we can add a line as follows.
# localhost name resolution is handled within DNS itself. # 127.0.0.1 localhost # ::1 localhost 192.168.224.53 cert-test.pi.com
Now accessing the PI on the browser will show that the connection is secure.
References
self-signed-wildcard-cert-for-ghes.md
Cisco Prime 3.4 / 3.5 / 3.6 / 3.7 / 3.8 / 3.9 Wildcard SSL-certificate Installation
Recent Comments